Responsible Disclosure
In the following, we present our hack on the Physical Security Information Management System “WinGuard” of Advancis Software & Services GmbH. We reported the vulnerabilities and findings listed here to the manufacturer within the framework of a responsible disclosure procedure.
Advancis reacted in an exemplary manner. We immediately got an appointment with the management and the head of development, were taken seriously as security researchers and were able to present our findings. This is not a matter of course. Many software companies still react reflexively, defensively and even threaten to sue.
At this point, a shout-out to Advancis: Your handling of white hats is exemplary! We’ll be happy to come back again 😉
Advancis has quickly fixed all the vulnerabilities mentioned below and provided customers with a comprehensive update. Basically, the vulnerabilities only existed if the WinGuard web server and/or the service access were activated in the settings. Affected are the versions WinGuard X4 Build 17.5 and lower. If you use WinGuard in your company, please make sure to have installed the current release.
How systems that should provide security themselves become a gateway for attackers
In this specific case, we are talking about a Physical Security Information Management System (PSIM) or threat management systems. These are used to process a multitude of messages and functions from subsystems more efficiently. Subsystems are typically:
- Intrusion detection systems
- Access control systems
- Electronic locking systems
- Video surveillance
- Fire alarm systems
- Fire extinguishing systems
- Outdoor security (motion detectors, fence monitoring)
- and much more.
PSIM systems are mostly used by companies that have implemented a large number of such security systems. These are usually companies with high or very high security requirements. By implementing a PSIM system, they aim to increase the level of security of their buildings, facilities and properties.
Employees in the security centre of such a company experience significant gains in effectiveness and efficiency through a PSIM system. By bringing all the subsystems together on one user interface, their control has become conceivably simple. (And hardly anyone has to deal with the subsystems themselves, which are often not very user-friendly).
If the fire alarm system reports a fire in the building, for example, the employee in the security control centre can, depending on the configuration, view the video image of the room with a mouse click. And thus verify whether there is actually a fire or merely a false alarm.
Another example from practice: someone wants to enter a location in the periphery, but has no access authorisation for this. Perhaps because the access takes place outside normal business hours. This should now be granted to him as an exception. Now, depending on the configuration, the employee in the security control centre can conveniently deactivate the intrusion alarm system for the area or the building open the necessary doors via the electronic locking system.
And this example, at the latest, makes you sit up and take notice. What would happen if such a PSIM system were controlled by malicious third parties? This question has been on our minds. Especially because PSIM systems are often used by operators of critical infrastructures (CRITIS). The reliable supply of energy and water, as well as other critical services according to BSI-KritisV, is a fundamental building block for our social peace. If the security of CRITIS were to be compromised by inadequately secured PSIM systems, this could have fatal consequences.
Focus on the market leader
The PSIM system “WinGuard” from Advancis Software & Services GmbH is used worldwide and is one of the most advanced solutions on the market. On its website Advancis writes:
“Physical Security Information Management (PSIM) is a software platform that integrates multiple unconnected security systems and controls them from a comprehensive user interface. This enables the user to fully understand and optimally resolve situations as they arise.”
This description coincides well with how we also perceive PSIM and how we ourselves have described it above. Furthermore, Advancis states:
“With WinGuard, we define PSIM+ as a solution that goes beyond the known scope and offers cross-trade integration of the entire building, communication and IT infrastructure. The connection to higher-level operational control systems is also an enhancement compared to classic PSIM systems.”
Advancis is obviously endeavouring to network as many relevant systems as possible and is also penetrating areas that originally have little to do with building and plant security itself. Advancis’ goal is to increase the benefits for the operator. But it is clear: the higher the degree of networking of systems, the higher the risk that can result from a single weak point.
The search for vulnerabilities in WinGuard
We have not received any funding or grants for our security research. We conduct our security research out of pure curiosity and in the interest to motivate manufacturers to improve their products by uncovering security vulnerabilities.
Advancis themselves talk about an increased IT security standard, which they want to achieve with the following measures, among others:
- Encryption used (TLS and AES).
- Possibility of redundancy
In order to verify these statements, we have examined WinGuard for possible vulnerabilities. Security problems that are not relevant in practice were ignored. This includes, for example,Information disclosure.
The experimental setup
The challenge in setting up an experimental environment is always to design as realistic a simulation of an attack as possible.*
Our setup:
- Blackbox test: we had no knowledge of the source code, nor of system architecture.
- We only used information from publicly available documentation.
- We limited ourselves to a local WinGuard installation. After all, an attacker will not have a large test network with various interfaces at his disposal.
All this was done under the premise that the attacker can communicate with the WinGuard server.
Exploring the attack vectors
One of WinGuard’s strengths is that it can connect a multitude of subsystems. For almost every common security system, WinGuard offers a suitable interface. From the perspective of an attacker, however, exactly these interfaces are particularly interesting. Because each of them offers him a potential access to the system.
Before we examined the interfaces to subsystems, however, we wanted to dedicate ourselves to the even more promising interfaces for controlling WinGuard. These include, among others, the web server and the service interface.
Finding 1: The web server
Web servers are typically exposed to the outside world and accessible to attackers even when they are not on the internal network. Accordingly, we chose an experimental setup according to the following scheme:
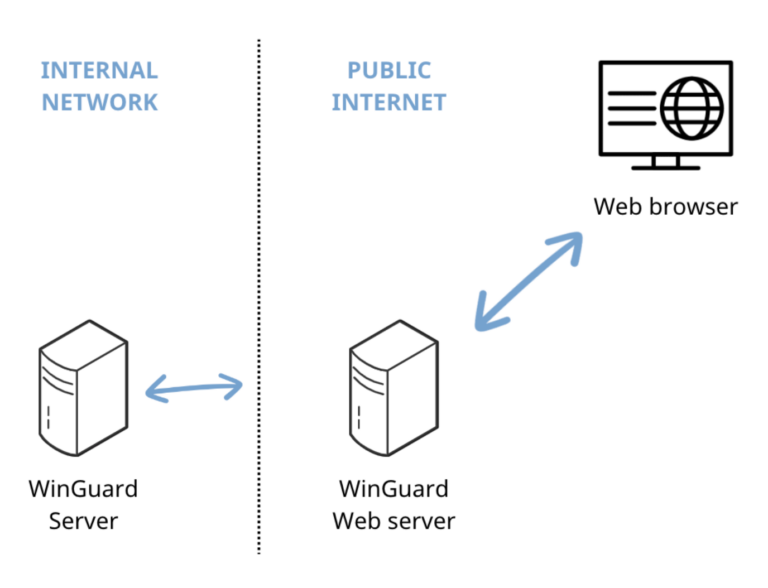
In this case, an attacker could not attack the WinGuard server directly, but would have to attack the WinGuard web server first.
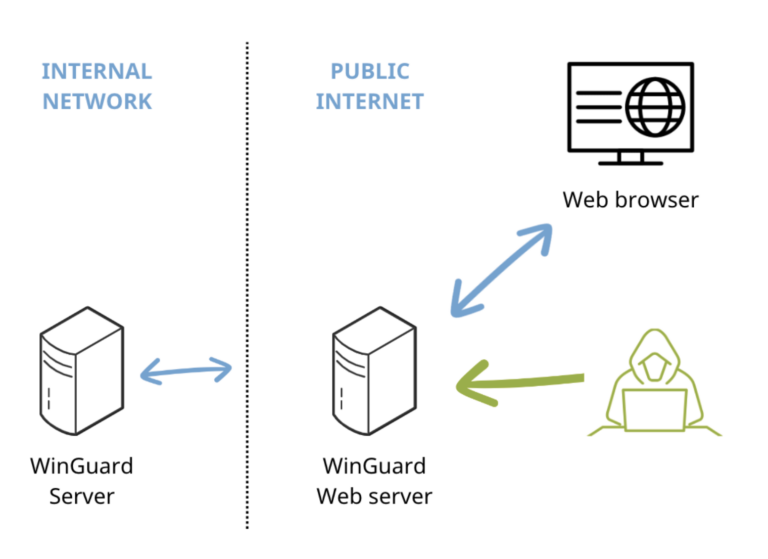
Accordingly, we started our attack with the web server. This delivered, as far as usual, files for the WebApp (JS, HTML, CSS,…).
In addition, the web server provided a “websocket” server. The web application itself is delivered by the web server, but then communicates with the “websocket” server.

An example from this communication:
{“method”:”login”,”params”:{“username”:”Benuter1″,
“password”:”Geheim”,”language”:”de”,”workstation”:
“Web”,”type”:”web”},”Id”:3}
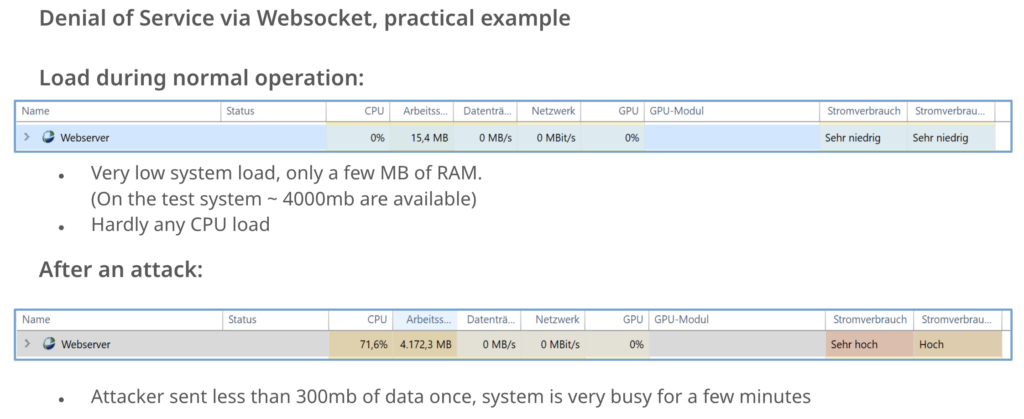
Denial of Service via “Websocket” Server
If the web server is no longer accessible, the user will not be able to access WinGuard via this way.
Denial of Service attacks are a widespread approach. In this “classic approach”, the attackers send millions of useless requests. The web server is busy with these requests and in this state no longer allows access for regular users.
However, there are also a number of problems for the attacker with this approach. For one thing, he would have to have a very good network connection, at least one that is better than the attacked system. Secondly, the attacker’s IP can simply be blocked (e.g. in the firewall settings). In such a case, the load on the web server would immediately return to normal and its accessibility for users would be restored. However, there is an interesting bug in the websocket function:
{“method”:”GetSettings”,”params”:{“keys”:[]….
The WinGuard server executes the command as follows:
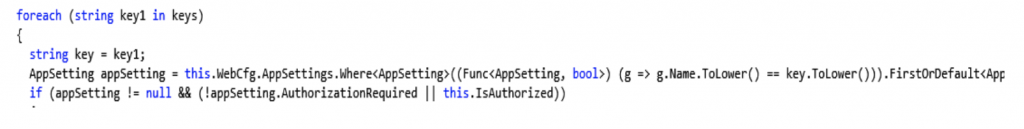
The problem here is that no length check of the parameter “Keys” is carried out. This makes a Denial of Service possible.
If the attacker sends many empty keys, they are loaded into the memory without being checked by WinGuard and kept there. Due to the WinGuard memory structure, it is sufficient if the attacker sends a few megabytes of data to completely fill the memory.
The “classic” problems of a Denial of Service described above were thus solved from the attacker’s point of view. The attacker’s network connection no longer played a role, since the few megabytes of data could also be transmitted without any problems, e.g. via the mobile network. Blocking the attacker’s IP address was also ineffective, as WinGuard was already busy when the data was sent once.
Finding 2: WinGuard Service Access
After the web server, we have turned our attention to the service access. If this interface is activated in the configuration, several security problems arise at once.

Via the settings, protection against brute force attacks can be set in WinGuard. At first sight, the service access seems to be uninteresting for attackers, because
- it is only a monitoring interface
- it makes no difference whether you log in as user or as admin
- the settings cannot be changed
Presumably, Advancis has not taken comprehensive protective measures for the service access for the same reasons. This was certainly the case with the client login.
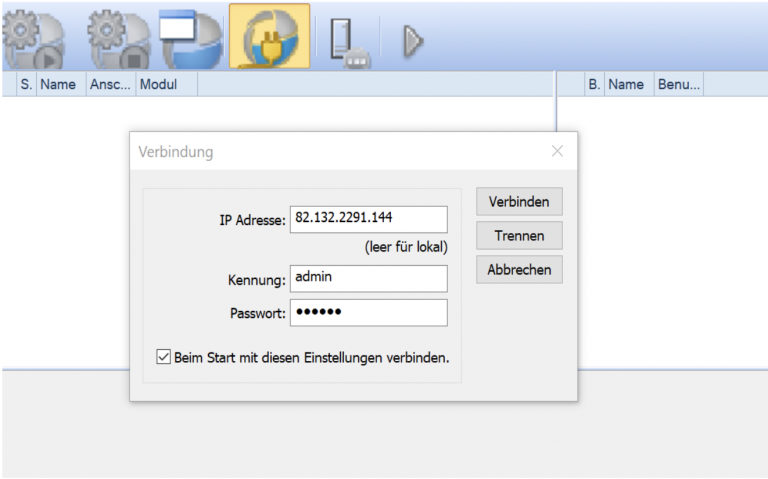
However, it was noticeable that there were no special users for service access. This led to the assumption that the same user credentials were valid for the service access as for the clients.
We therefore directed the brute force attack at the service access and were able to determine that, in contrast to the client, it had no brute force protection.
The service access used its own protocol, which is not publicly documented. However, the bit-by-bit analysis of the transmitted data revealed that no encryption was used.
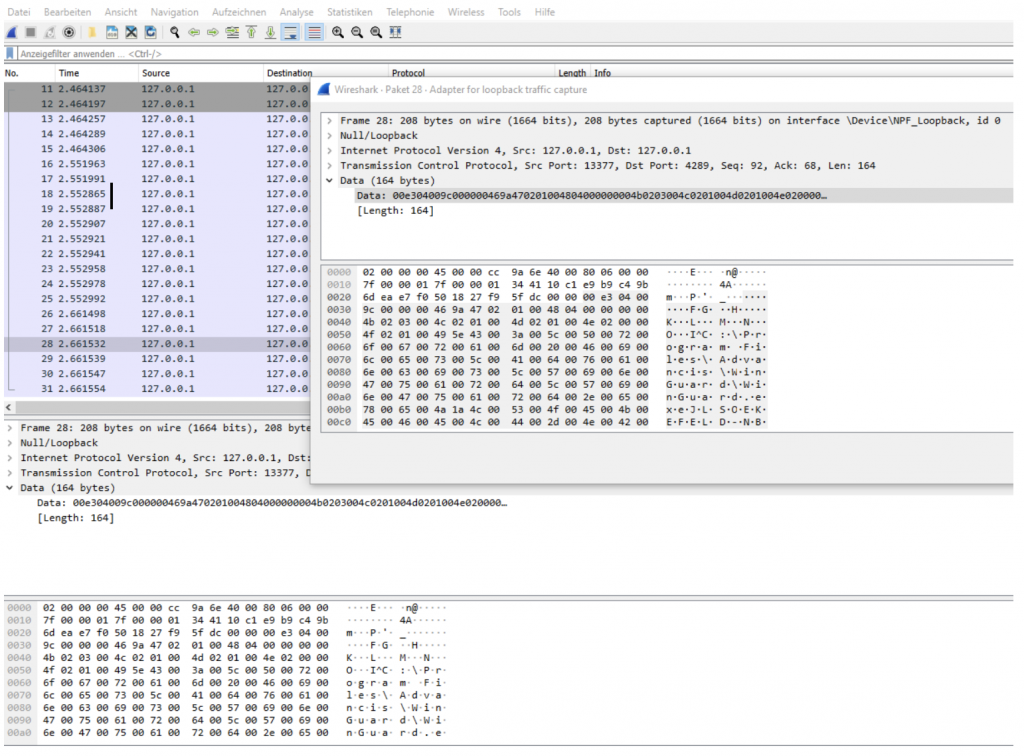
The lack of encryption enabled attackers to simply read passwords in the network. The system did not provide for encryption at this point, i.e. it could not be activated at any point, as the following screenshot of the service panel interface shows:
In this case, common network sniffers (e.g. Wireshark) were sufficient to obtain the password in plain text.
With the findings from the protocol analysis, we developed a programme that tries passwords for a user account. In this way, we were able to try several thousand password attempts per second. For this, we established four simultaneous connections to the server. Depending on the network connection, this number can be increased. Of course, this depends on the position of the attacker in the network.
We tailored the word lists with passwords to our target using common programmes (crunch, cewl).
User Enumeration
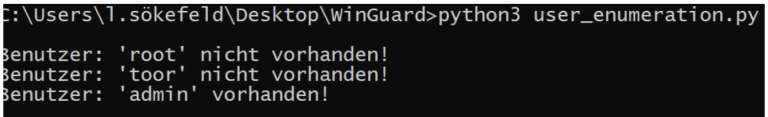
In addition to the password, we now of course need valid user names. It has been shown that WinGuard behaves differently with packages containing valid and invalid user names.
Example:
1st packet [user: root , password: dummy] → response: 24 bytes
2nd packet [user: toor, password: dummy] → response: 24 bytes
3rd packet [user: admin , password: dummy] → response: 1024 bytes
When we experimented with different usernames, we noticed that for valid users (here “admin”) the response is longer (here 1024 bytes) than for non-existent users (“root” and “toor”). With WinGuard, time seems to be a factor at this point, which is why the procedure was not completely deterministic. However, in tests with several hundred user names, there was an accuracy of > 90%. For our purposes, this was completely sufficient.
To identify valid user names, we developed another programme with the task of checking whether a certain user exists. The programme used a word list of possible user names and tried them out one after the other.
Result of our investigation
Our analysis has shown that at the time of our investigation, very practice-relevant security vulnerabilities exist in WinGuard, which could also have been used for a malicious attack. Depending on the configuration used (web server, service access), either the operation of WinGuard could be significantly disturbed (Denial of Service) or, even worse: The attacker could obtain login data by reading the network traffic or by simply trying it out. With these, the attacker could have controlled the system and all subsystems.
All’s well that ends well.
Advancis closed all vulnerabilities after our notification and provided customers with an update. The investigated vulnerabilities existed if the WinGuard web server and/or the service access were activated in the settings. Affected are the versions WinGuard X4 Build 17.5 and lower. If you are using WinGuard in your company, please make sure that you are using the latest version. In its Release Notes, the manufacturer Advancis also publishes all changes that have always been implemented in the latest WinGuard version, as well as further technical and enhancement information.
What our research shows again and again is that it is essential to keep an eye on physical security systems regarding your attack surfaces in cyberspace. Pay attention to your interfaces, or someone else may do it. Are your systems secure? We would be happy to check your security architecture for vulnerabilities!





